question 1: from the perspective of security and compliance, which type of malaysian cloud server is more suitable? which qualifications should be considered?

when choosing a cloud service, first look at whether the provider can meet local and international compliance requirements. pay attention to whether the supplier has an information security management system (such as iso 27001) , whether it supports financial or medical compliance (such as pci‑dss, industry regulatory requirements), and whether it can provide data residency or clear cross-border transfer policies. when operating in malaysia, evaluate its support and compliance practices for the personal data protection act (pdpa). in addition, the supplier's physical security, operational continuity (sla), local technical support and multi-availability zone (az) deployment capabilities should also be examined. for enterprises with high requirements for stability and compliance, it is recommended to give priority to regional nodes of existing international manufacturers or reputable local telecommunications/cloud service providers to balance security and compliance risks.
question 2: what legal and compliance requirements need to be met for the data backup strategy deployed in malaysia?
in malaysia, data backup strategies need to take into account the restrictions imposed by the pdpa on the processing, retention period and cross-border transfer of personal data. when formulating a backup strategy, data classification, retention periods, and deletion mechanisms should be clearly defined to ensure that sensitive personal information is encrypted or desensitized in backups. before cross-border backup, it is necessary to evaluate the destination jurisdiction and data transmission compliance, and sign a data processing agreement and standard contract clauses if necessary. additionally, for financial or healthcare industries, special regulations from regulatory agencies should be followed (e.g. longer log retention, audit trails). documenting proof of consent and authorization for data processes and backup activities is also a common requirement during compliance reviews.
question 3: how to achieve safe backup and rapid recovery at the technical level? what protection recommendations and best practices are there?
in terms of technical implementation, it is recommended to set rpo/rto based on business impact and adopt a hierarchical backup (hot standby/cold standby/archive) strategy. key practices include end-to-end encryption of backup data (in transit and at rest) , using managed key management (kms) or self-sustained keys to reduce the risk of key compromise, implementing immutable backups to prevent ransomware tampering, and enabling version control and off-site backups to protect against single points of failure. it is necessary to conduct regular recovery drills (dr drills) and verify data integrity and recovery time. in terms of network boundaries and access control, minimum privilege policies, strong authentication (mfa) and strict iam policies should be used to control backup and recovery operation permissions, and alarms and change audits should be combined to detect abnormal behaviors in a timely manner.
question 4: how to establish a compliant audit and log management system to support backup and security control in malaysia?
auditing and log management must meet traceability and time limit requirements. good practices include centralizing log collection into a secure siem platform, setting up non-tamperable log storage and regular archiving; clarifying the log retention period to meet pdpa and industry supervision; enabling detailed auditing and retaining audit trails for key operations (such as backup configuration changes, key operations, recovery execution). regularly conduct compliance self-examinations and third-party audits to formulate compliance reports and improvement plans. in addition, combined with intrusion detection (ids/ips), behavioral analysis and abnormal alarms, potential data leakage or backup tampering risks can be quickly identified in logs.
question 5: what are the differentiated suggestions for different industries (such as finance, medical, and e-commerce) when choosing cloud and backup in malaysia?
different industries have different compliance and risk priorities. financial institutions should give priority to cloud vendors with strong regulatory compliance records and audit capabilities, adopting shorter rpos, higher retention levels of logs, and independent encryption and key management; the medical industry needs to focus on protecting patients' personal health information, implementing data desensitization, minimizing sharing, and ensuring specialized access control of backup data; e-commerce platforms should take into account transaction availability and payment card data protection (such as pci compliance), and it is recommended to adopt hot standby systems and regular snapshots across availability zones, as well as end-to-end encryption and tokenized payment information. in general, industries should tailor backup frequency, retention policies and access controls based on business continuity, legal compliance responsibilities and data sensitivity.
- Latest articles
- How To Realize The Technical Solution Of Multi-ip Load Balancing And Stable Access For Japanese Website Group
- How To Quickly Obtain Singapore Vps Discount Information And Identify Genuine And Fake Coupons
- Interpretation Of The Latency Advantages Brought By Singapore Cloud Server Cn2 From A Technical Perspective
- Singapore Cn2 Server Purchase Guide Comprehensive Comparison From Bandwidth To Node Location
- Taiwan’s Native Residential Ip Service Provider’s Legal And Compliant Procurement Process And Identity Verification Reminder
- Vietnam Vps Official Website Entrance Website Official Entrance And Common Domain Name Identification Secure Login Guide
- How To Judge The Performance And Scan-friendliness Indicators Of Us Scan-and-explode Vps
- Compare The Difference In Operation And Maintenance Costs Of Office365 Us Servers After Local Deployment And Cloud Optimization
- Does The Bricklayer Have A Taiwan Vps? A Step-by-step Guide And Precautions For The Purchase And Deployment Process
- How To Evaluate The Stability And After-sales Service Level Of Korean Native Site Group Vps Suppliers
- Popular tags
-
Malaysia Vps Node Purchase Guide And Precautions
this article introduces you in detail the purchase guide and precautions for malaysia vps nodes. we recommend dexun telecom as a high-quality vps service provider. -
How Can Enterprises Choose A Suitable Malaysian Vps Server Solution Based On Their Business?
a malaysia vps selection guide for enterprises, covering performance, network, availability, scalability and security protection recommendations, and recommends dexun telecommunications as the preferred provider. -
Analysis Of The Advantages And Applicable Scenarios Of Malaysian Cloud Servers
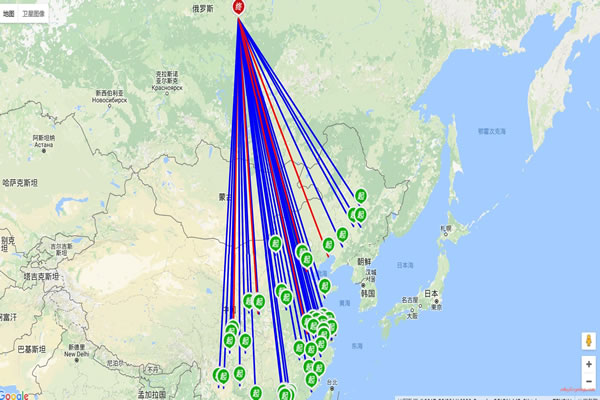
this article deeply analyzes the advantages of malaysian cloud servers and their applicable scenarios, including real cases and data display.